

Cloud adoption has grown rapidly. Although cloud computing is now considered to be mainstream, security-related cloud adoption challenges persist. Cloud security is very important for any organization, irrespective of size, and digital engineering teams should always check from the get-go that their service providers can provide the correct security levels for their cloud workload. Because security is such an essential element of an organization’s cloud service, it is up to organizations, working in partnership with their cloud service provider, to really understand the different security roles, responsibilities, tools and best practices.
Getting the balance right security-wise is getting easier. Take, for example, AWS which has published its cloud security best practices to help customers implement cloud services in a highly secure manner. This help provide a steer to organizations unsure of the tools or services they require. The AWS cloud platform allows customers to scale and innovate while maintaining a secure environment. Customers only pay for the cloud security services they are using without any upfront expenses, unlike the on-premises environment.
When it comes to cloud security SNAFUs, misconfigurations that accidentally and unnecessarily expose services are the biggest culprits. Any misconfigurations during implementation can potentially lead to huge damage down the line. In the cloud, resource provisioning, management, and monitoring happen via APIs, console, and CLI. So, it’s essential to secure all these connections during the early stage of cloud adoption.
In addition, teams must ensure that virtualization, identity, and access management (IAM), workload protection, and network security and encryption are a part of this architecture blueprint. We are all familiar with catastrophic data breaches that make the news, but there are many others that do not, and the vast majority of these are avoidable. Let’s examine the following three scenarios, all derived from real experiences, and the look at how the vulnerability could have been avoided.
Case 1: Passwords matter
The account was compromised due to a weak root user password, combined with MFA not being configured. An attacker removed EBS, EC2 instances, S3 data backup, and asked for a ransom to provide the database backup file.
This could have been prevented by utilizing an IAM user with a specific policy instead of using the root account.
Case 2: Visible access keys
The developer posted the development account credentials for the AWS access and secret access key in the script, which was on the public git repository. Using those keys enabled the attackers to deploy multiple resources in all regions and created lots of dummy resources. For the six to eight hours that the account was hijacked, the attackers racked up a bill of $4,000-5,000.
This could have been prevented by using an IAM role instead of hard-coding the access keys into code. Access keys should be rotated periodically.
Case 3: Mis-configurations
The security group was not properly configured. In particular, port 22 was allowed globally, ports 80 and 443 were also open from all. The application which was hosted on EC2 instance was front-ended by the application load balancer. The attackers found a basic cross-site scripting vulnerability and SQL injection, tried injecting malicious scripts, and removed all the data from the server.
This could have been prevented by following a trusted advisory, putting WAF on top of the application load balancer, and utilizing the AWS inspector for security assessments.
These three cautionary tales are all examples of where a small security vulnerability caused big losses, and they all demonstrate how easy it would have been to deploy the secure cloud option. Hindsight is a wonderful thing, but it is even better to avoid making the error in the first place. Below we have compiled our 11-step guide to understanding security best practice structures and how users should implement the AWS platform and its services in the best way.
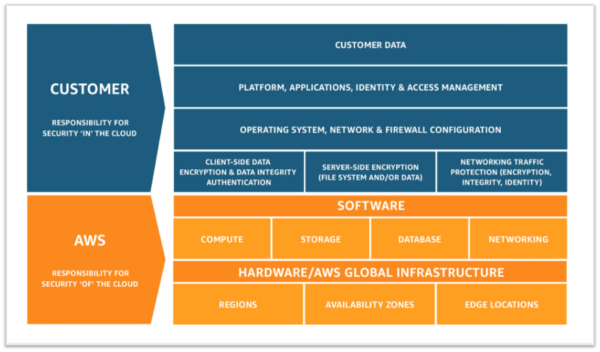
Step 1: Understand the Shared Responsibility Model
Step 2: Follow IAM Best Practices Including –
Step 3: Manage OS-Level Access and Keep EC2 Instances Secure
Step 4: Encryption!
Step 5: Follow Security Best Practices for AWS Database and Storage Services
Step 6: Network Security
Step 7. Web Application Security
Step 8. Enable Configuration Management
Step 9. Monitoring and Alerting
Step 10: Compliance
Step 11: Training and Certification
If you have any questions surrounding the cloud security best practice guidelines, or you have additional security queries, get in touch with Apexon. Let us know your toughest security dilemma, and we’ll help you solve it.