Over the last 15 years or so, a connected society has essentially become the platform on which we run our lives, with the average person co-existing in both the digital and physical space. As a result, we have become comfortable with the idea of confirming who we are to gain virtual access to a plethora of goods, services, banking, retail therapy and work apps.
And while this digital convenience has made our lives simpler, it has also been an open invitation to those with both malicious intent and a desire to profit from what can often be a relaxed attitude to online security. In fact, cyberattacks are so common in the modern world that it is extremely likely that we only pay attention when they directly impact us.
For that reason alone, it is critical that the companies and organizations that we trust to keep our data secure have authentication processes in place to keep the black-hatted hackers out. A recent survey by Gartner said that cybersecurity was a top priority for IT decision makers, with the analyst forecasting that 61 percent of surveyed CIOs expected to increase their risk management spending in 2021.
There is never a bad time to talk about how a robust attitude to user authentication can help companies maintain their duty of care to the workforce and, inevitably, their customers.
With that in mind, this blog post will walk you through some of the various stages of the business-to-customer enterprise identity services provided by Microsoft Azure.
For the purposes of this exercise, you will be required to have an Azure account. If you don’t have one, you can create one by clicking here.
Understanding Universal Identity
According to Microsoft, more than one billion dollars is invested in cybersecurity research and development by the company every year. As part of its investment, Microsoft also has over 3,500 security experts on its payroll. To put it simply, security is a huge priority for the tech behemoth, and they want you to know it.
And while Microsoft Azure is the cloud platform, the services and products that fall under its umbrella are intended to be “future ready.” For example, the business-to-customer identity element is provided by Azure Active Directory B2C (Azure AD B2C), with the idea being that consumers use their preferred social, enterprise or local account identities to gain single-sign-on access to a company’s applications and APIs.
Azure AD B2C is a CIAM solution that can handle millions of users and billions of authentications per day. The directory manages the authentication platform’s scaling and security, monitoring and automatically responding to threats like as denial-of-service, password spraying, and brute-force attacks.
This focus allows companies to not only manage the requisite elements of authentication and security but also access built-in threat-intelligence and premium features. Without further ado, let’s dive into the steps required to authenticate users in Azure AD B2C.
Create an Azure AD B2C Tenant
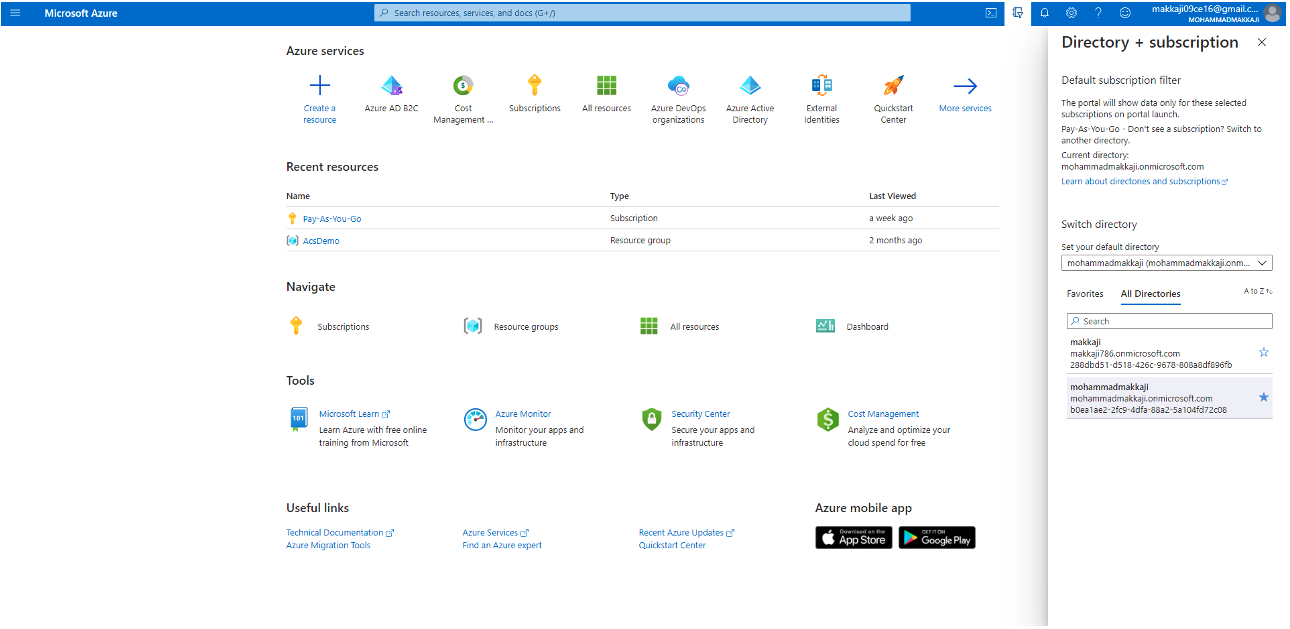
- Log in to the Azure AD portal. Please ensure that you sign in with an Azure account that has at least the contributor role or a subscription resource category assigned to it.
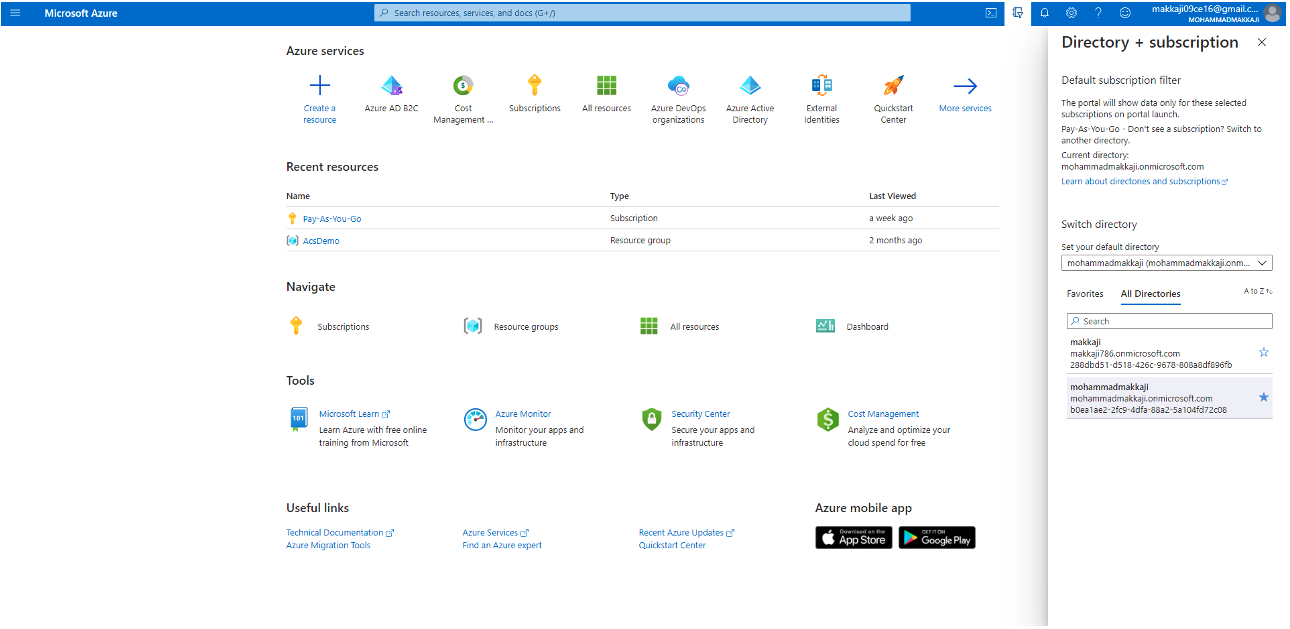
- Choose the directory in which your subscription is stored.
- Select the Directory + Subscription icon in the Azure portal toolbar, and then the directory that includes your subscription. Note that this directory is distinct from the one where your Azure AD B2C tenant will be stored.
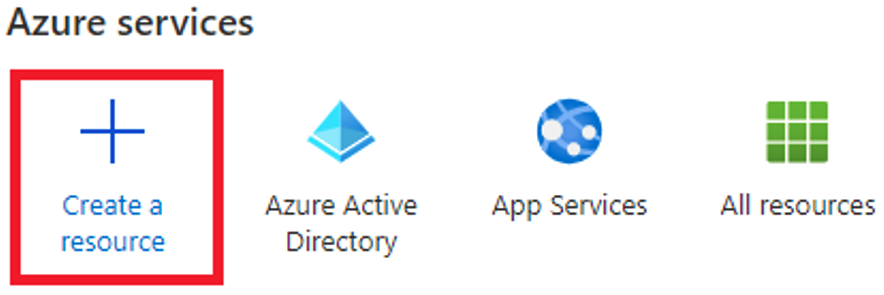
- Pick Create a resource from the Azure portal menu or the Home tab.
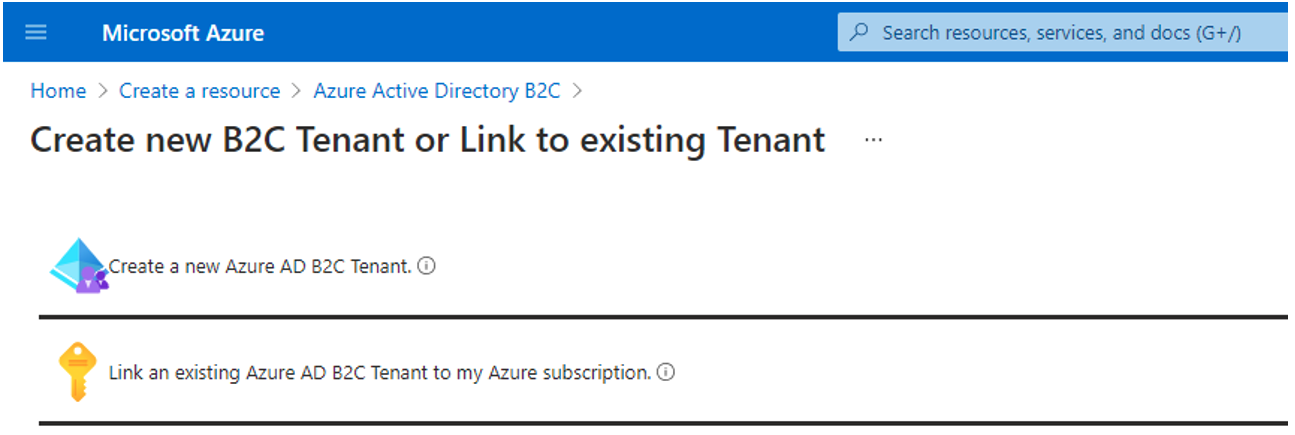
- Select Create after searching for Azure Active Directory B2C.
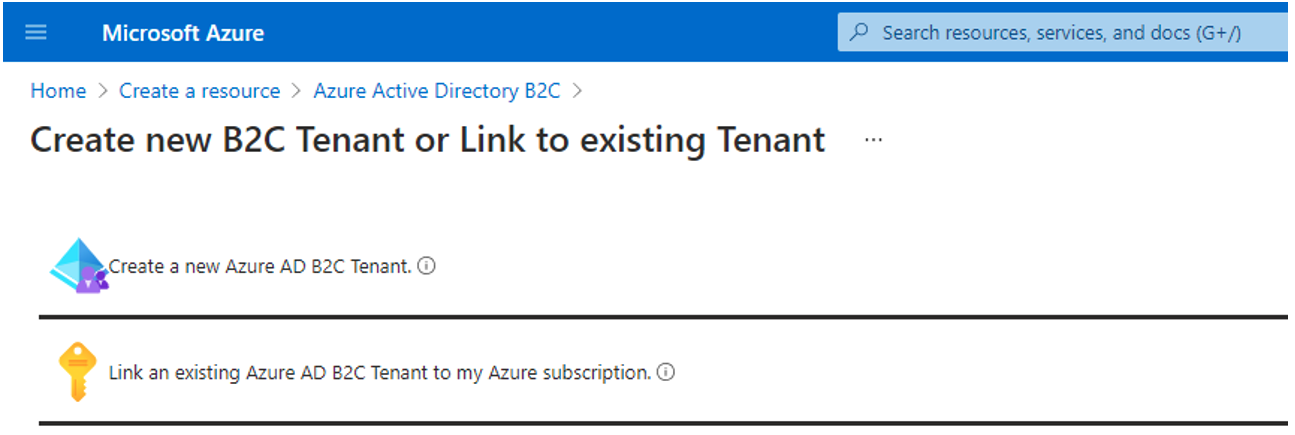
- Choose Create a new Azure AD B2C Tenant from the drop-down menu.
- On the Create a directory page, enter the following:
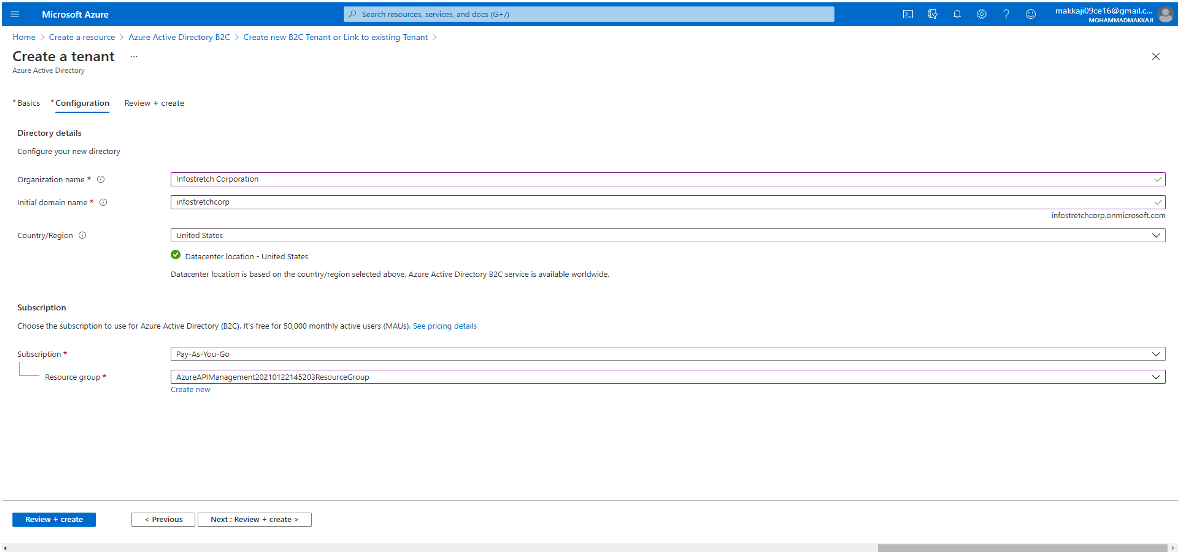
- Organization name – Enter a name for your Azure AD B2C tenant.
- Initial domain name – Enter a domain name for your Azure AD B2C tenant.
- Country or region – Select your country or region from the list. NB: This selection cannot be changed later.
- Subscription – Select your subscription from the list.
- Resource group – Select or search for the resource group that will contain the tenant.
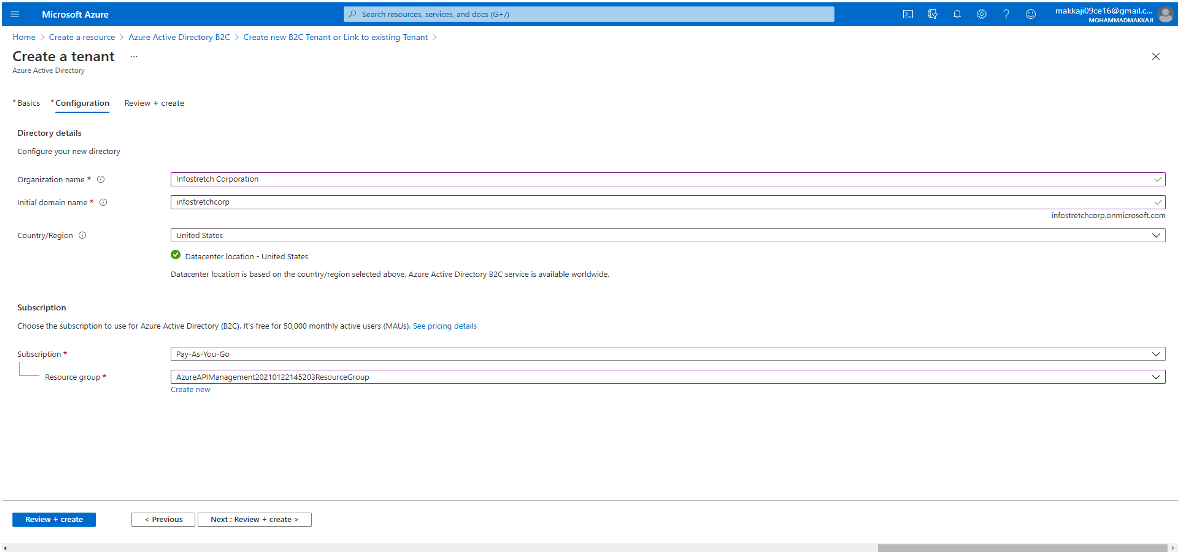
- Select Review + Create.
- Examine your directory options. Then choose Create. For the purpose of resolving implementation issues.
You should also be aware of the following elements:
- For billing purposes, you can connect multiple Azure AD B2C tenants to a single Azure subscription.
- To attach a tenant, you must be an administrator in the Azure AD B2C tenant and have at least the Contributor position assigned to your Azure subscription.
- A subscription must be linked to an Azure AD B2C tenant.
Once you have completed these steps, you should be good to go.
Select your B2C Tenant Directory
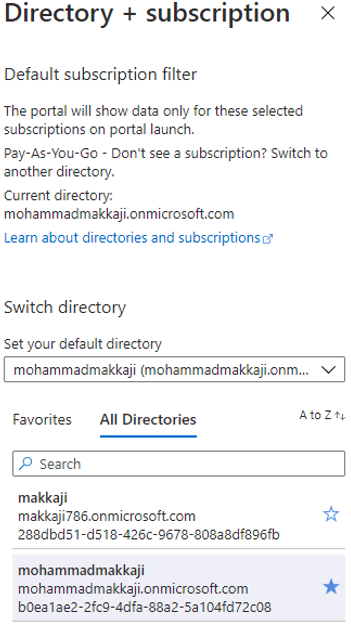
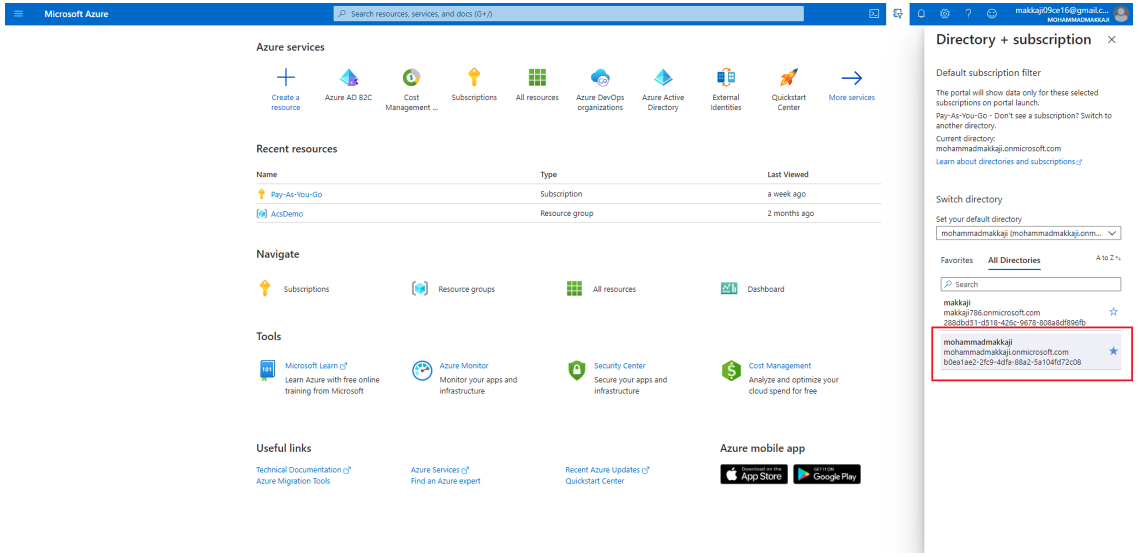
To begin using your new Azure AD B2C tenant, navigate to the directory where the tenant is stored.
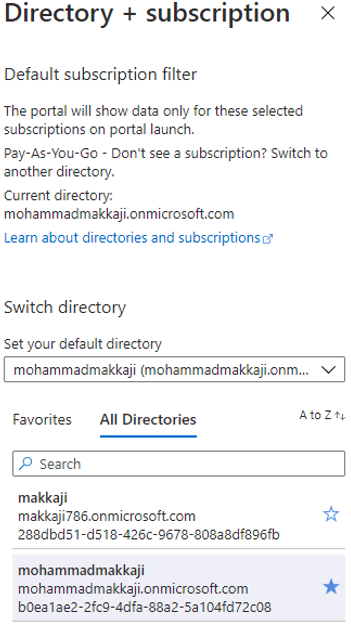
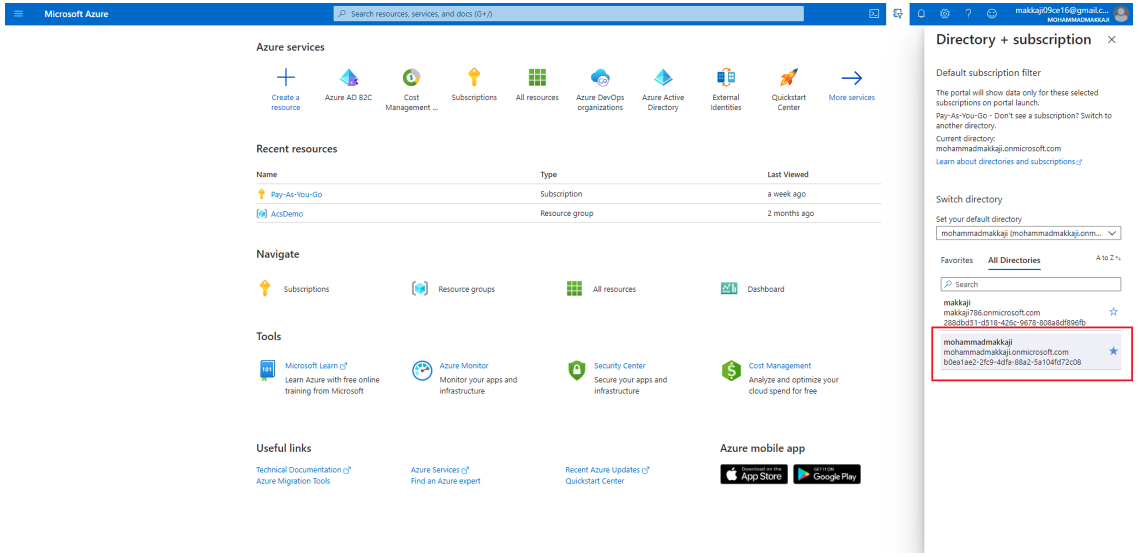
In the Azure portal’s top menu, pick the Directory + subscription filter, then choose the directory that contains your tenant.
If your new tenant does not appear in the list at first, refresh your browser window and then pick the above filter in the top menu again. You can see how this should look in the visual below:
Optional: Add Azure AD B2C as a Favorite
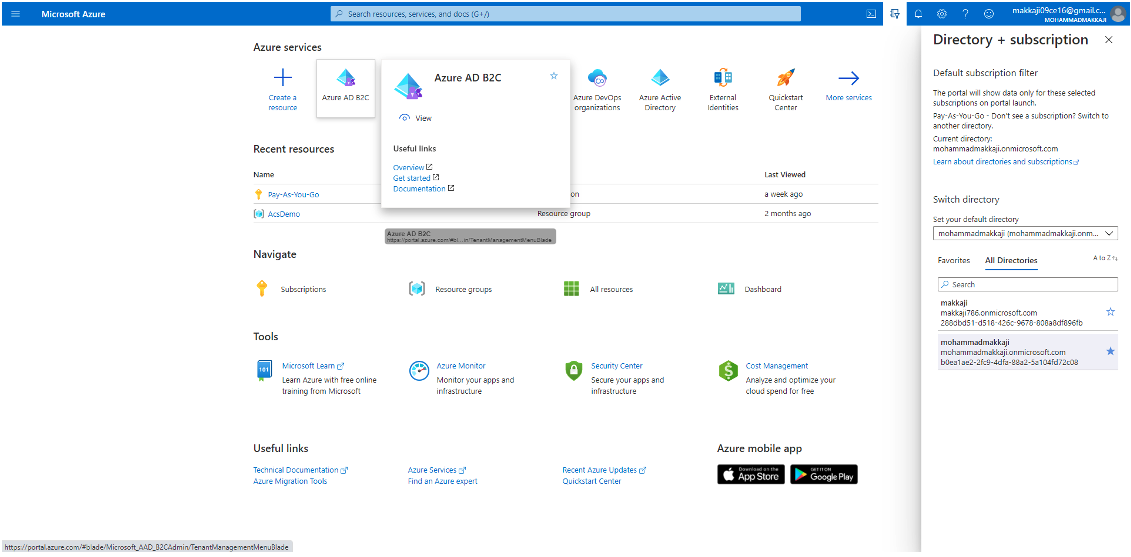
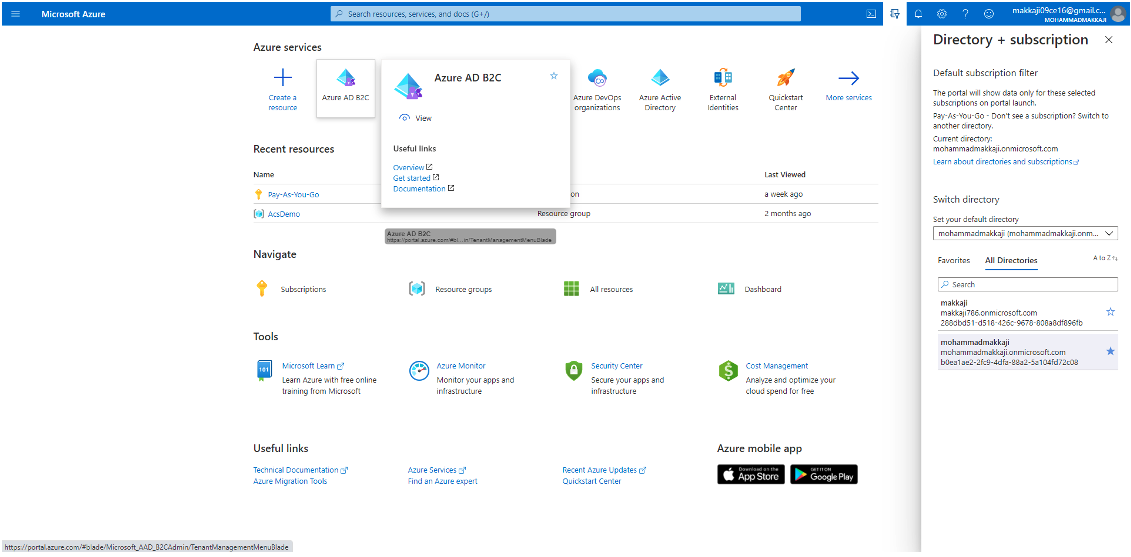
This optional action makes it easier to choose your Azure AD B2C tenant in the walkthroughs that follow.
We recommend that you bookmark Azure AD B2C instead of looking for it in All Services any time you need to work with your tenant. By doing this and accessing the portal menu’s Favorites section, you will find it easy to navigate to your Azure AD B2C tenant.
This process just needs to be done once. Just make sure you’ve moved to the directory containing your Azure AD B2C tenant as mentioned in the previous section, select your B2C tenant directory, and then proceed as follows:
- Log in to the Azure portal.
- Select All services from the menu.
- Check for Azure AD B2C in the All-services search box, hover over the search result, and then pick the star icon in the tooltip. Azure AD B2C is now included in the favorites section of the Azure portal.
- If you want to move your new favorite up or down, go to the Azure portal menu, pick Azure AD B2C, and then drag it to the desired location (as shown below).
Register a Web Application in Azure AD B2C
Your applications must be registered in a tenant that you control before they can communicate with Azure AD B2C. This walk-through will show you how to use the Azure portal to register a web application.
For the purposes of this tutorial, an “internet application” is a typical web application in which the server handles most of the application logic. Frameworks such as ASP.NET Core, Maven (Java), Flask (Python), and Express may be used to build them (Node.js).
As we noted above, you will need to have an Azure account to register a web application. You will also need to build your own Azure AD B2C tenant (if you haven’t done so already), but you can use a pre-existing tenant if you have one.
For the record, you can use our latest unified App registrations experience or our legacy Applications (Legacy) experience to register a web application in your Azure AD B2C tenant. This can be achieved as follows:
- Log in to Azure.
- In the portal toolbar, click the Directory + Subscription button, and then choose the directory that contains your Azure AD B2C tenant.
- Check for and pick Azure AD B2C in the Azure portal.
- Select App registrations, then New registration from the drop-down menu.
- Give your application a name. For instance, consider webapp1.
- Pick Accounts in any identity provider or corporate directory under supported account forms (for authenticating users with user flows).
- Pick Web under Redirect URI, and then type https://jwt.ms in the URL text box. Please be aware that:
- The redirect URI is the endpoint to which the authorization server (in this case, Azure AD B2C) sends the user after it has completed its contact with said user, and to which the user receives an access token or authorization code if authorization is effective.
- It’s usually a publicly available endpoint where your code is running in a production application, such as https://contoso.com/auth-response. Set it to https://jwt.ms, a Microsoft-owned web application that shows the decoded contents of a token. Note that for testing purposes, the contents of the token never leave your browser.
- As an alternative, you could add the endpoint where your app listens locally during app creation, such as https://localhost:5000. At any time, you can add or remove redirect URIs from your registered applications.
- In addition, the following restrictions apply to redirect URIs:
- The reply URL must begin with the scheme https.
- The reply URL is case-sensitive. Its case must match the case of the URL path of your running application. For example, if your application includes …/abc/response-oidc as part of its path, do not specify …/ABC/response-oidc in the reply URL. As the web browser treats paths as case-sensitive, cookies associated with the former may be excluded if redirected to the case-mismatched latter.
- Select the Grant admin consent to open ID and offline access permissions, then check box under Permissions.
- Select Register.
Create a Client Secret
- Select the application you made – for example, webapp1 – in the App registrations tab.
- Pick Certificates and secrets from the left menu’s Manage
- Choose New client secret from the menu.
- In the Summary box, write a description for the client secret – Clientsecret1, for instance.
- Select a valid period for the secret under Expires, and then select Add.
- Write down the value of the password. In your application’s code, you use this value as the application password.
Enable ID Token Implicit Grant
The implicit grant is distinguished by the fact that tokens such as ID and access tokens are returned to the application directly from Azure AD B2C.
You can enable the implied grant flow in the app registration for web apps that request an ID token directly from the authorization endpoint, such as ASP.NET Core web apps and https://jwt.ms. To do this, follow these simple steps:
- Select Authentication from the Manage menu on the left.
- Select both the Access tokens and ID tokens check boxes under Implicit
- Choose Save.
Create UserFlows in Azure AD B2C
You can have user flows in your applications that allow users to sign up, sign in, or manage their profiles.
In your Azure AD B2C tenant, for example, you can build multiple user flows of various types and use them in your applications as appropriate. User flows can be reused in different apps.
In this section, you’ll learn how to build a user flow for:
- Sign-up and sign-in
- Editing profiles.
- Password resets.
Using the Azure portal, this tutorial demonstrates how to build some suggested user flows. As a prerequisite, you will need to register the applications in the user flows that you want to create.
Create a Sign-up and Sign-in User Flow
In a single configuration, the sign-up and sign-in user flow manages both sign-up and sign-in interactions. Depending on the background, the app’s users are guided in the right direction. The process of creating this authentication tool is as follows:
- Log in to Azure.
- In the portal toolbar, click the Directory + Subscription button, and then choose the directory that contains your Azure AD B2C tenant.
- Check for and pick Azure AD B2C in the Azure portal.
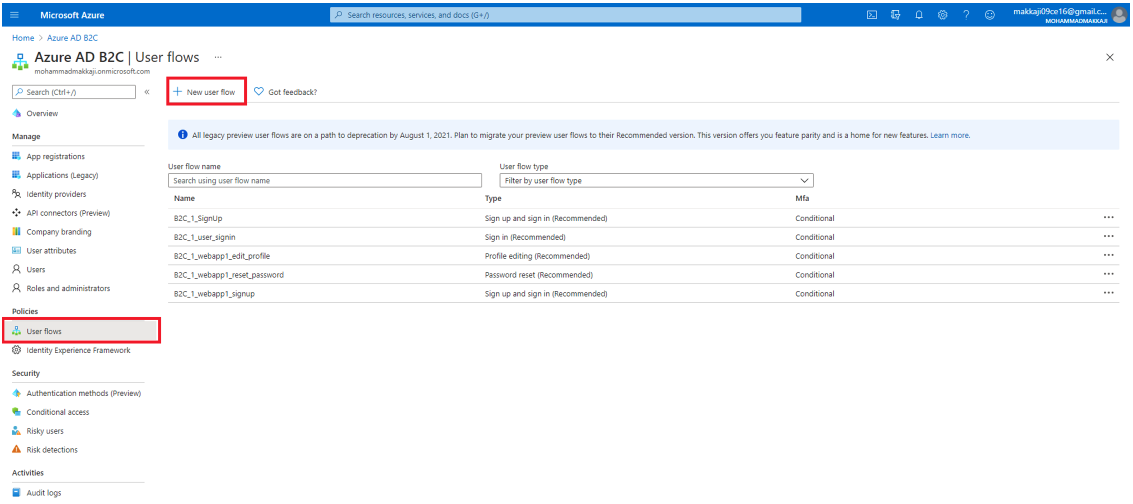
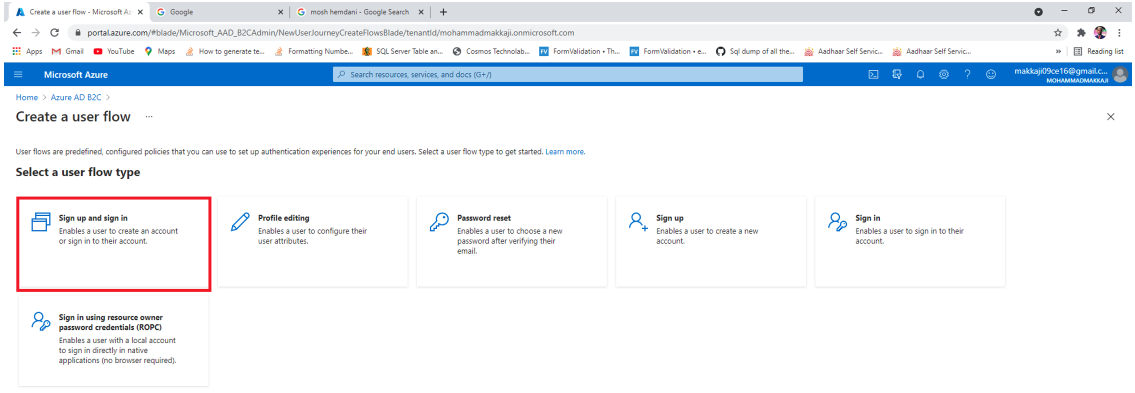
- Pick User flows from the Policies menu, then New user flow.
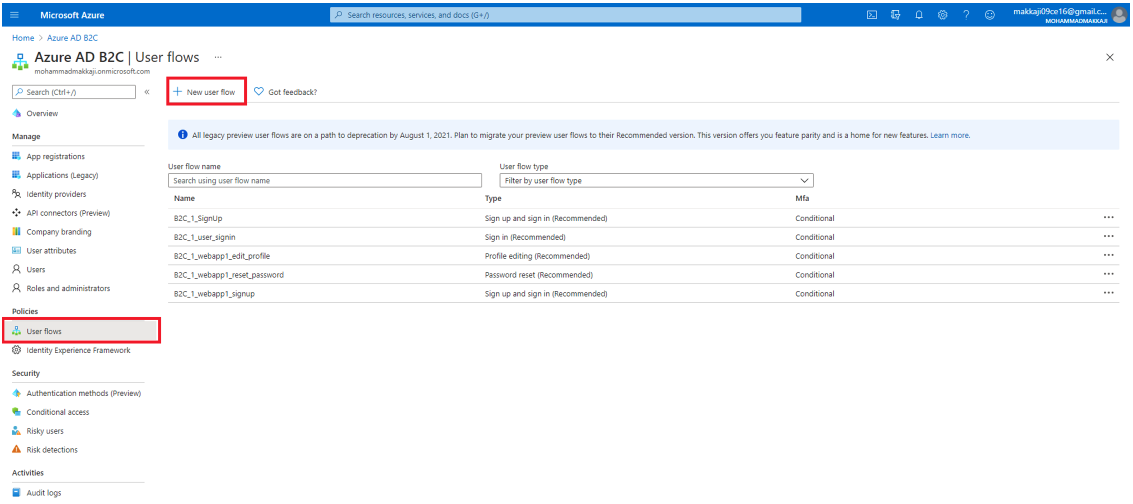
- Select the Sign up and sign in user flow on the Create a user flow tab.
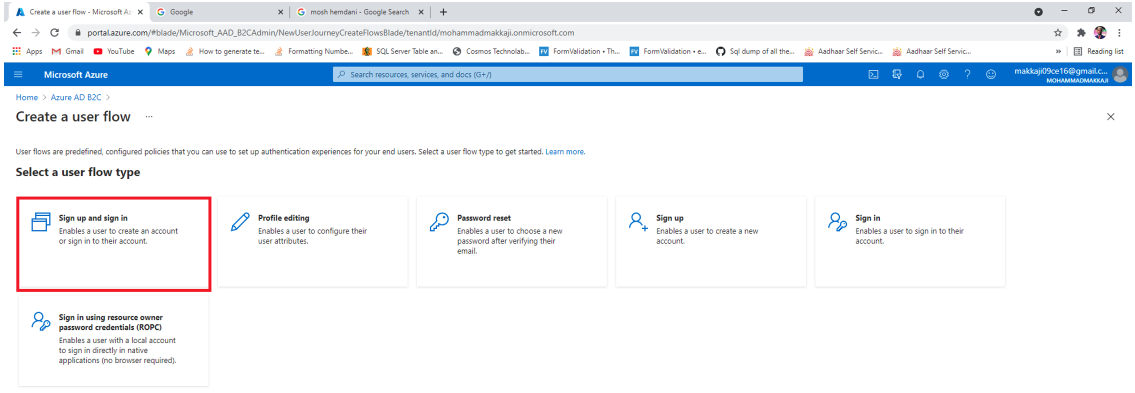
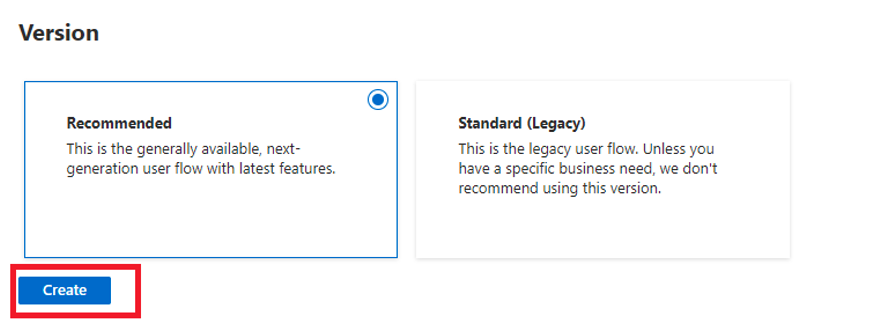
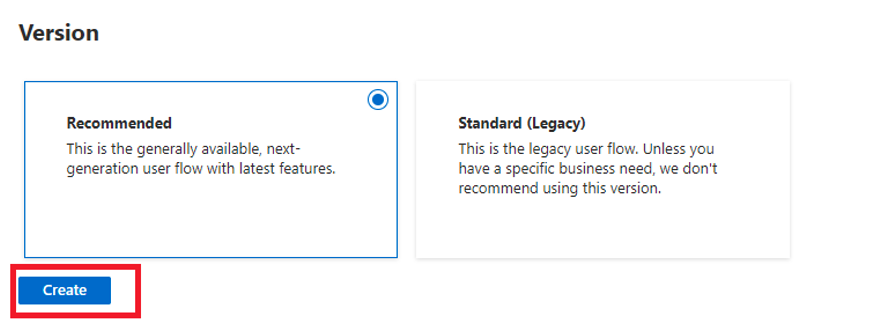
- Click Recommended under Select a version, and then Create. The different variants of user flows are specified, as per the visual below:
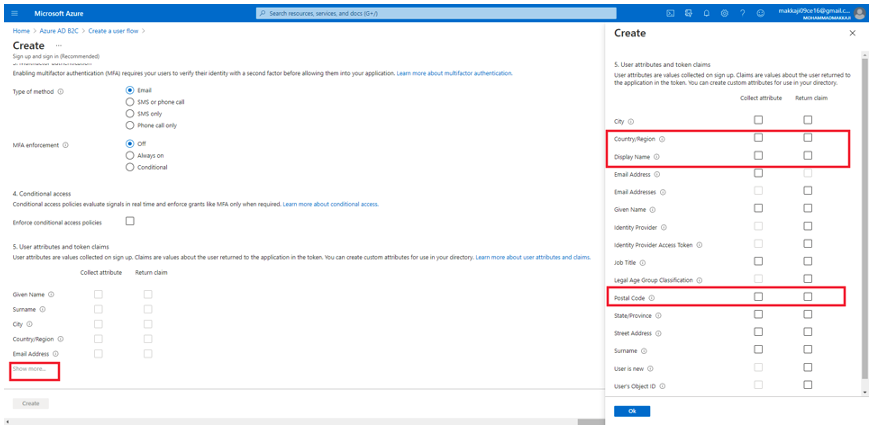
- Give your user flow a name – Signupsignin1, for example.
- Select Email signup for Identity Providers.
- Choose the statements and attributes that you want to obtain and submit from the user during sign-up in User attributes and claims. For example, you can choose attributes and claims for Country/Region, Display Name and Postal Code, for example. Once you have chosen the attributes, you can click the OK button.
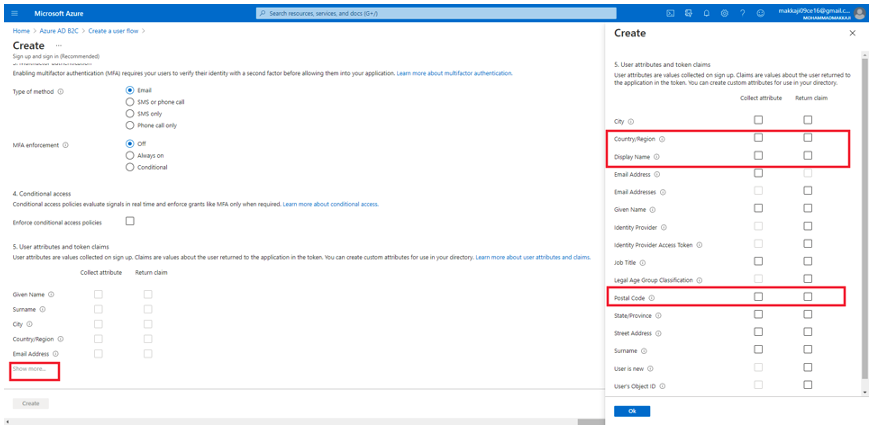
- To add a user flow, click Create. The name is immediately prefixed with the B2C 1 prefix.
Test the User Flow
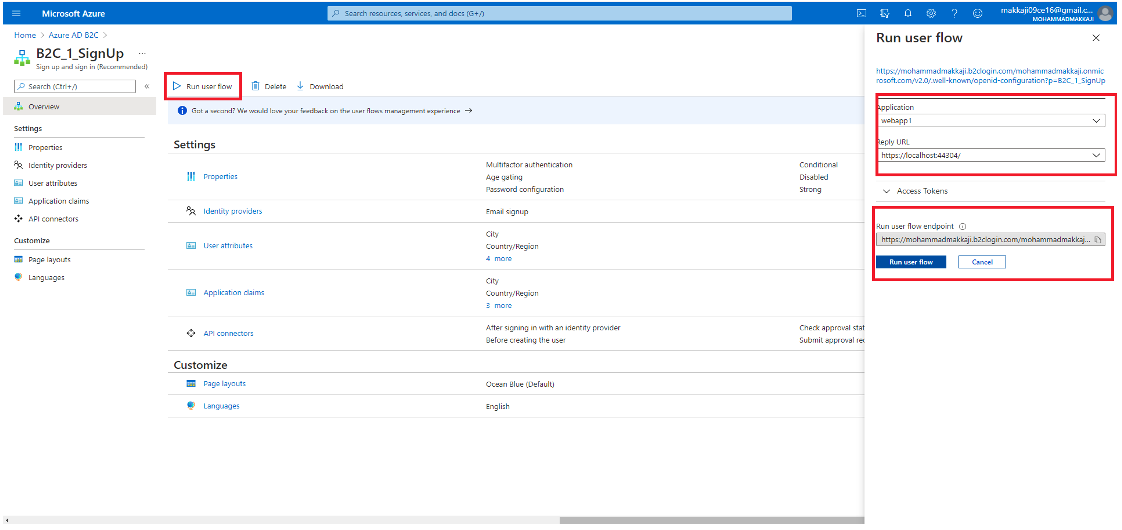
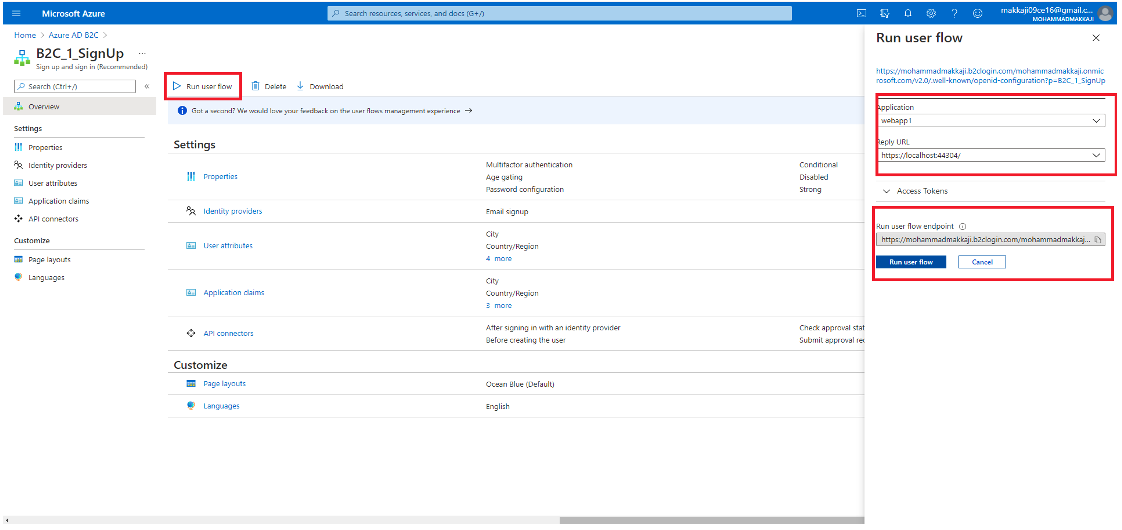
- Open the overview page for the user flow you built, then select Run user flow.
- Select the web application called webapp1 that you previously registered for Application. The URL for the reply should be https://jwt.ms.
- Select Sign up now after clicking Run user flow.
- Enter a valid email address, click Send verification code, type in the verification code received, and then click Verify code
- Create a new password and double-check it.
- Select your country and area, then type in the name you want to appear, along with a postal code, and click Create. The token is sent back to https://jwt.ms and should appear on your screen.
- You can now re-run the user flow, and you should be able to log in using the account you made. The returned token contains the claims of country/region, name, and postal code that you chose.
Create a Profile Editing User Flow
This user flow enables users to edit their profile in your application.
- Pick User flows from the menu on the Azure AD B2C tenant summary tab, then New user flow.
- Choose the Profile editing user flow on the Create a user flow tab.
- Select Recommended from the Select a version drop-down menu, then Create.
- Give the user flow a name – profileediting1 works here.
- Pick Local Account Sign in for Identity Providers.
- Choose the attributes that you want the consumer to be able to edit in their profile under User attributes. Allocate all attributes and statements for elements such as Display name and Job description, for example, by selecting Show more. Click the OK
- To add the user flow, click Create. As in other user flows, the name is immediately assigned with the B2C 1 prefix.
Test the User Flow
- Open the summary page for the user flow you built, then select Run user flow.
- Pick the web application called webapp1 that you previously registered under Application. The URL for the reply should be https://jwt.ms.
- Select Run user flow, and then sign in with the account you built earlier.
- You can now modify the user’s show name and job description. Continue by pressing the Enter key. The token is sent back to https://jwt.ms and should appear on your screen.
Create a Password Reset User Flow
A password reset user flow is used to allow users of your application to (no surprises here) reset their password.
- Pick User flows from the Azure AD B2C tenant overview menu, then New user flow.
- Select the Password reset user flow on the Create a user flow
- Choose Recommended from the Select a version drop-down menu, then Create.
- Give the user flow a name – Passwordreset1, for example.
- Permit Reset password using email address for Identity Providers.
- Select the claims you want returned in the authorization tokens sent back to your application by clicking Show more under Application claims – you can select User’s Object ID, for example.
- Click OK.
- To add the user flow, click Create. For reference, the name is immediately prefixed with B2C 1 prefix.
Test the User Flow
- Open the summary page for the user flow you built, then select Run user flow.
- Pick the web application called webapp1 that you previously registered under Application. The URL for the reply should be https://jwt.ms.
- Select Continue after verifying the email address associated with the account you previously built.
- You can also update the user’s password. Pick Continue after changing the password. The token is sent back to https://jwt.ms and should appear on your screen.
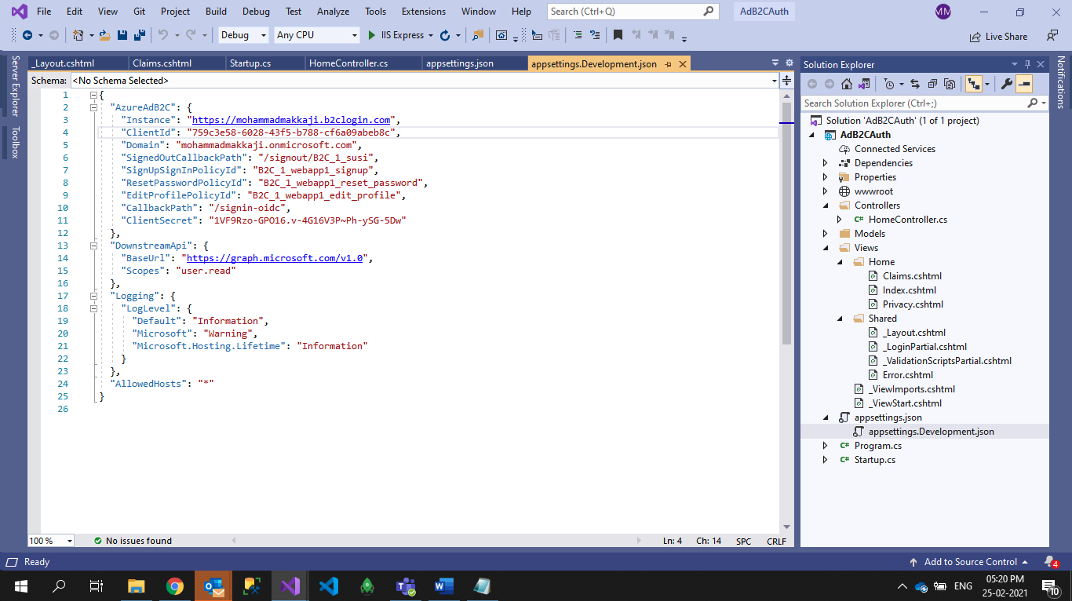
Implementation in ASP. Net Core Web Application
The final walk-through shows you how to use Azure AD B2C to authenticate users in an ASP.NET web app. This will allow you to authenticate to social accounts, enterprise accounts and Azure AD accounts via open standard protocols. A full tutorial from Microsoft can be found here, but these are the basic steps to follow.
-
-
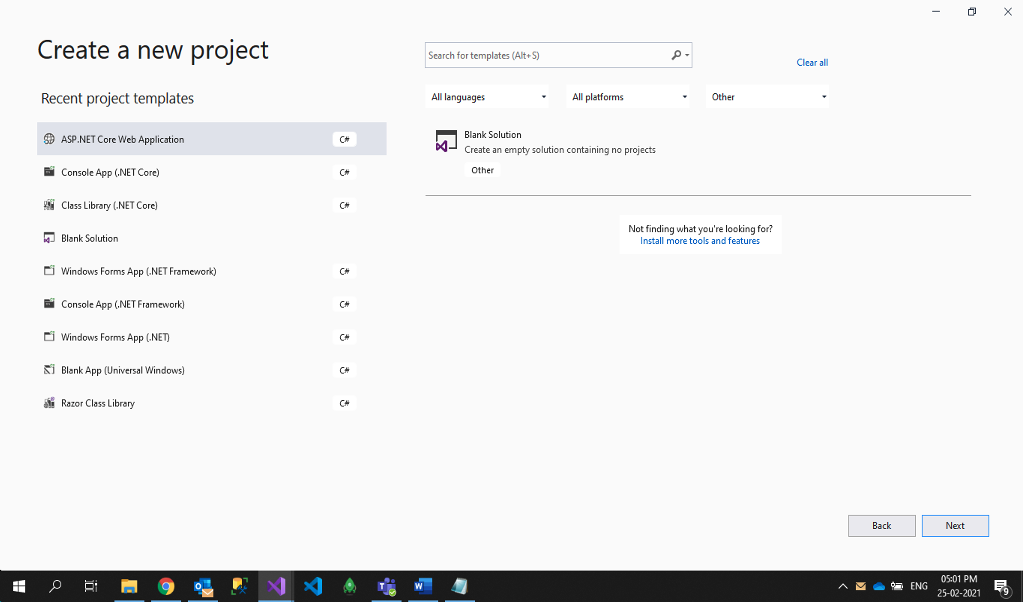
Create a new ASP. Net Core Web Application
-
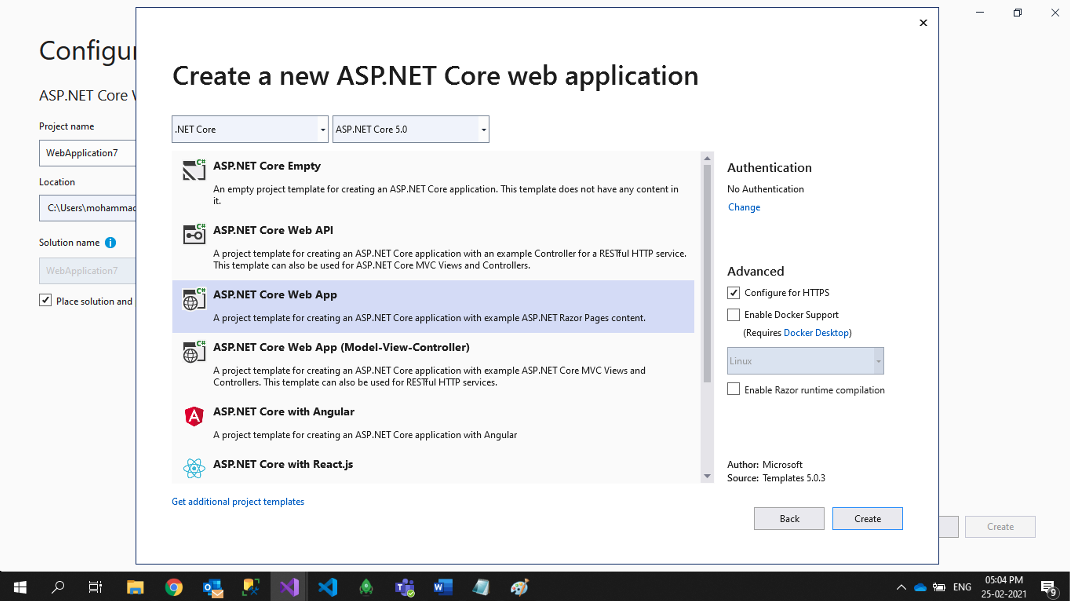
Click on Net Core Web App
-
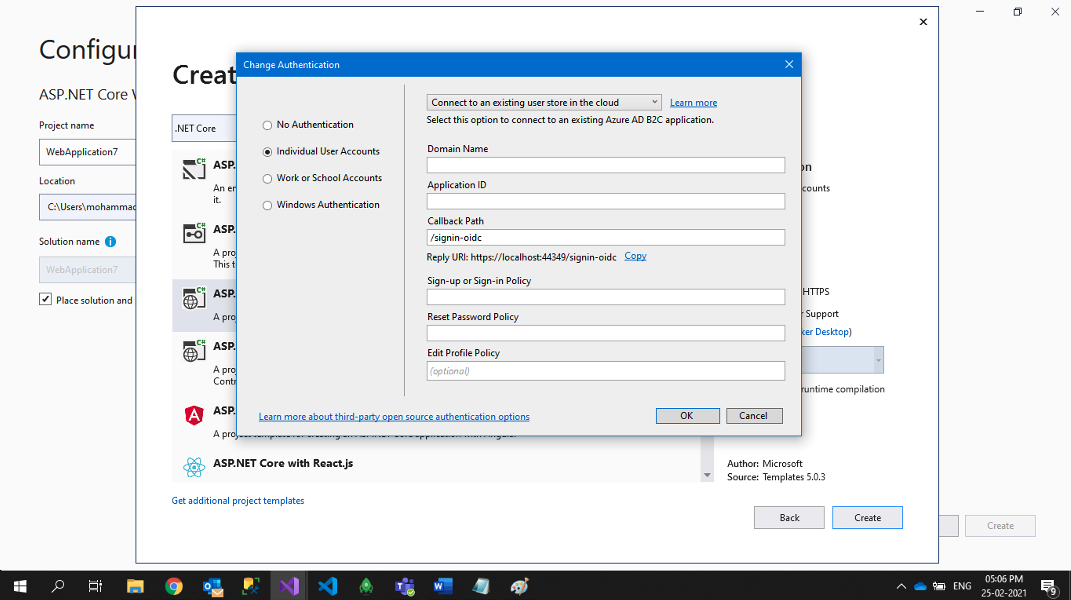
Click on Change Authentication option
-
Click on Individual User Accounts and select Connect to an existing user stored in the cloud and fill in the required details from the Azure portal created earlier.
- Domain Name: Your B2C tenant domain
- Application ID: Application in which you created the B2C Tenant
- Callback Path: /signin-oidc
- SignIn or SignUp Policy: relates to the required user flow created earlier
- Reset Password Policy: relates to the Reset Password user flow which you created
- Edit Profile Policy: refers to Edit Profile user flow which you created
-
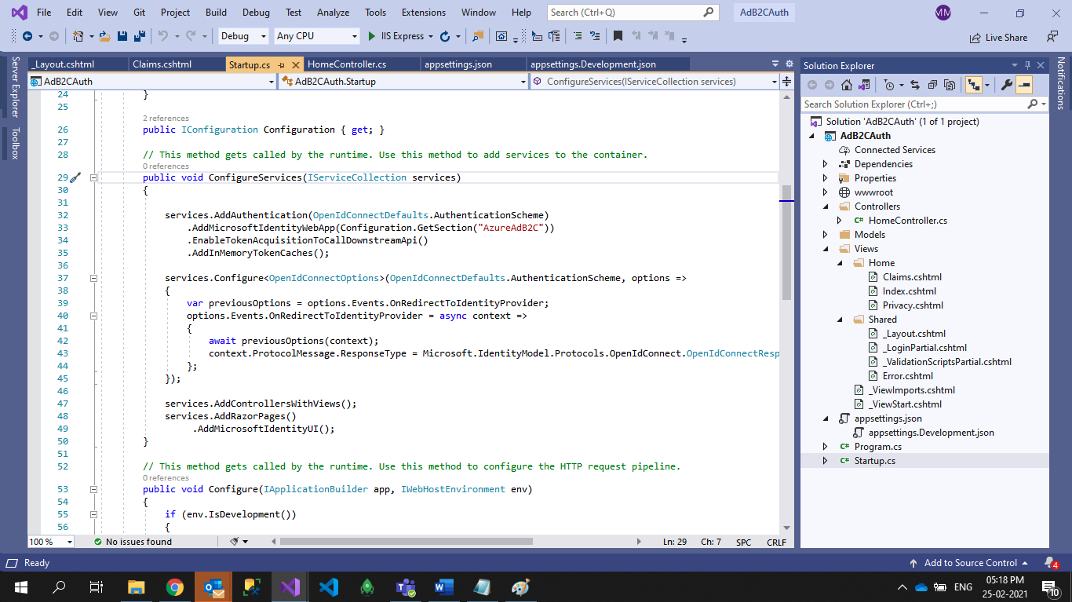
Click on OK, Create Application and Add Below Configuration Code in StartUp.cs file
-
Change the configuration in json file with your generated values
-
Finally, you should select Run Application and click on the Sign In and Sign Up button
End Result: A Fully Functional Azure B2C Service
As we discussed at the beginning of this blog post, authentication processes are a critical part of security touchpoints and end user access.
The steps that we have walked though are part of a fully functional Azure B2C service solution that will allow users to create and, importantly, log into their accounts. In the connected society, making that process both simple but secure will go a long way to maintaining trust and, importantly, ensuring that the digital experience is seamless for every end user.
To find out more about how Apexon leverages Microsoft Azure in developing your digital journey or cloud engagement, please contact us today. Alternatively, you can read more about our cloud solutions here.
Also read: Keycloak: Unlocking Seamless Identity and Access Management for Enterprises